This professionals series looks at the top-notch experts working at PayPay.
For this installment, we spoke with Nobuaki Nakazawa, Acting Senior Manager of the CISO Office, which is responsible for PayPay’s information security.
We will introduce both the charm of Nakazawa-san, who other members describe as an “absolute pro,” and PayPay’s information security.

Nobuaki Nakazawa
CISO Office, Legal & Risk Management Division
Experience: Worked for 10 years at a systems integrator, developing open systems, OS kernels, and compilers. His strength in low-layer technology led him to become a security engineer. From there, he has about 10 years of experience in penetration testing, artifact analysis, and cybersecurity consulting for e-commerce and FinTech businesses. Since joining PayPay in December 2019, he has mainly been responsible for the Cyber Attack Control (Red Team) and Security Monitoring Office (CSIRT, SOC) while leading the security strategy for the entire business.
Self-Learning Implementation and Creating a Satisfying Security Environment
Tell us about your background and why you joined PayPay.
I joined PayPay in December 2019, about a year after the PayPay app was rolled out in 2018 when the company was about to organize a full-fledged information security team. Prior to joining PayPay, I worked as a security checker and consultant for a security vendor. I’ve seen security holes everywhere in information systems, so I was skeptical about the FinTech retail format, but when I made my first payment with PayPay as a user, I was genuinely impressed by how fast the transaction was, and that’s when I decided I wanted to join the company.
What is unique about PayPay’s CISO Office?
There are five major roles (units) in the team. Because these five units coordinate well, they help the business evolve assertively while maintaining overall business security.
- Promotion and Training Unit
- In charge of internal security, device security, training/awareness, announcements
- Regulations and Audit Response Unit
- Organizes internal rules, responds to internal/external audits of global standards, acquires internationally recognized certifications, and oversees/audits supply chains
- CSIRT Unit
- Responds to, investigates, and oversees security incidents and events, such as information leaks and phishing attacks
- SOC Unit (aka Blue Team)
- Monitors internal and external communications and behavior of the entire system and detects attacks and irregularities 24/7
- Red Team Unit
- Consists of white hats who attack the PayPay system, attempting to break in and detect critical problems before criminals do
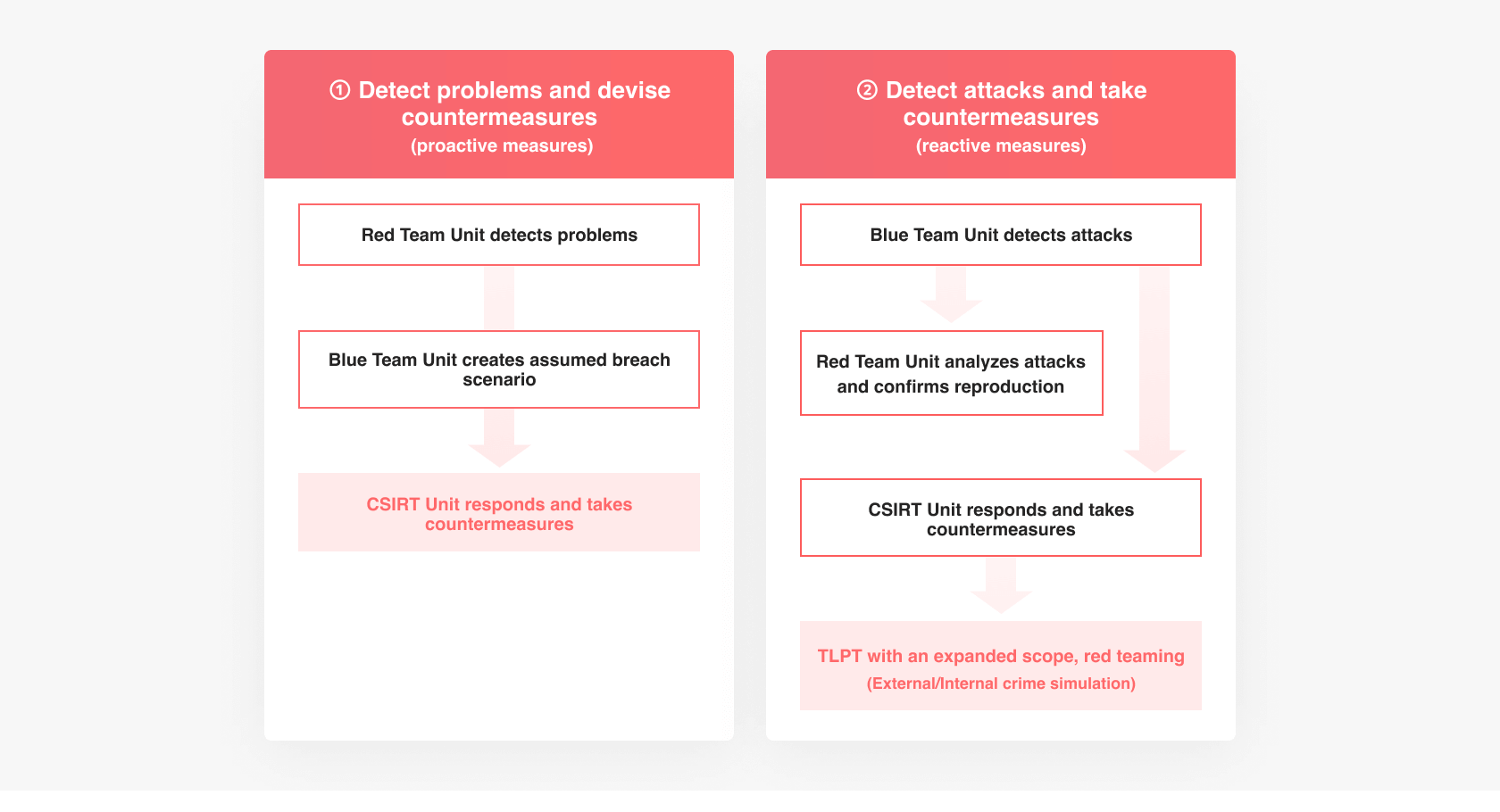
Within that framework, I am in charge of the Red Team Unit, CSIRT Unit, and SOC (BlueTeam) Unit, which all deal with cyberattacks, and I oversee the design and building stages. In addition to general security measures, the key point in building the units is to always be aware of the presence of attackers. Our boss, CISO Kato, is very calm and collected, but he was previously a corporate officer at YJFX and has been involved in the FinTech business for a long time. And since we are a payment service provider, the level he requires of the CISO Office is exceptionally high. His commitment led to the organization of five units, which are constantly being strengthened.
Building a red team and CSIRT units
While I have proposed to and helped build red teams, CSIRTs, and SOCs for management departments during my time as a consultant at a security vendor, I had no experience building them myself at a company. I felt that by doing it myself, I would finally be able to really grasp the difficulties and challenges that come with it, so I looked for a company where I could make that happen. During a job interview for PayPay, I heard from Kato-san that he wanted to build a red team in-house, so I said, “Let me help out!” and we hit it off from there. After joining the company, I built the Red Team Unit using my experience and with the help of my team members while constantly learning the parts that I needed to actually build myself.

I then built the CSIRT Unit, the team responsible for investigating and analyzing security issues as they arise. Information security and cybersecurity are both integral parts of doing business on the internet. In the event of a security incident, though highly unlikely, everything that all PayPay employees have worked so hard to create can disappear in an instant. That’s why all units in the CISO Office have made it their mission to ensure that we don’t lose public confidence and cause a major blow to business.
Protection against various threats

PayPay mainly operates online payment businesses, so we face various threats. There are many types of risks, including system shutdowns due to unauthorized access and reputational risks that follow such events. Attacks and incidents like information leaks threaten business credibility. Other threats include financial crimes such as ATO (account takeover) and fraud, or even internal misdeeds. To counter all such possible risks and continue to provide business safely and smoothly, the three units mentioned above tightly cooperate as described below.
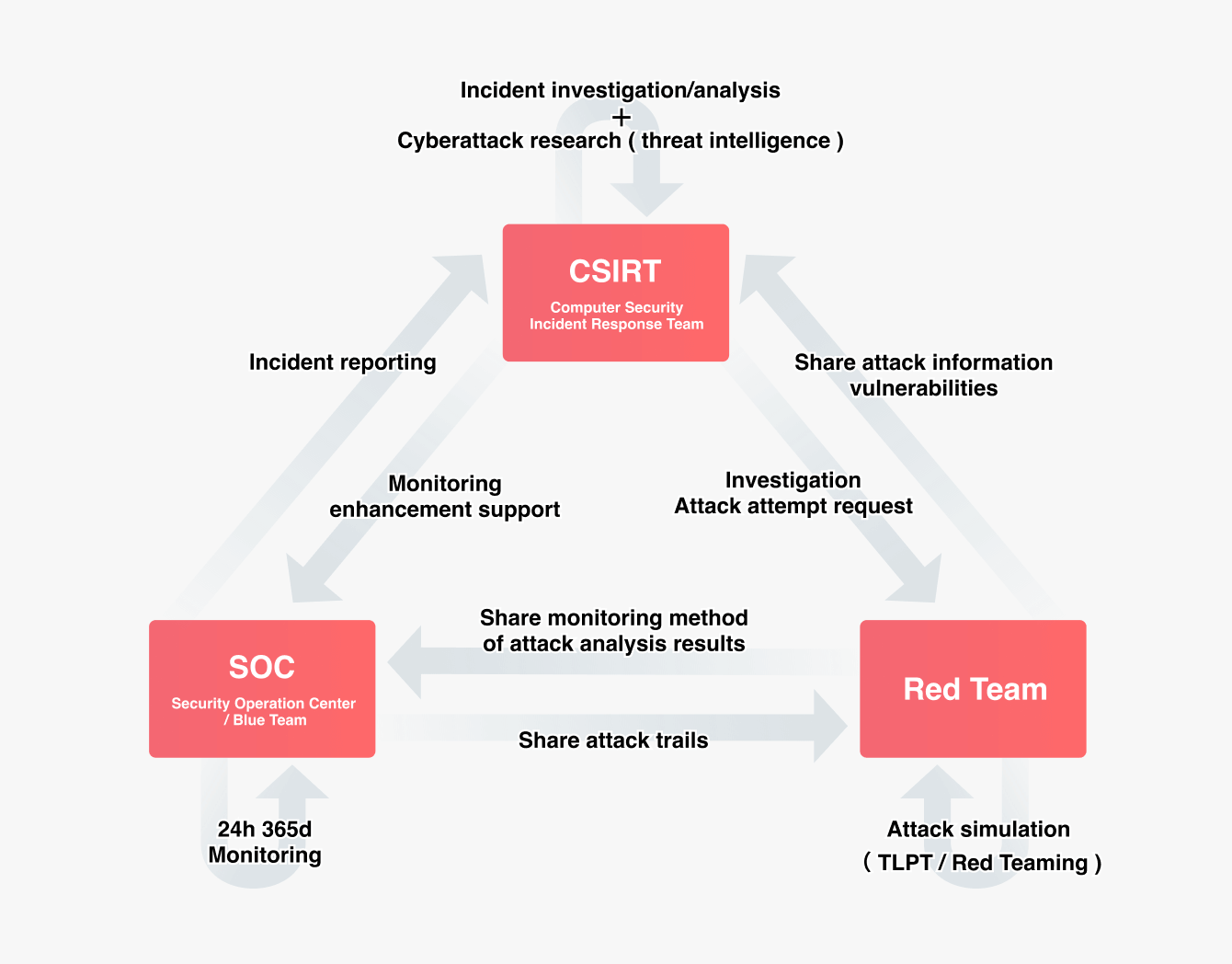
Another essential task is for researchers to constantly collect the latest information and attack information from technical literature, online articles, social media, etc., to consider what kind of attacks may be carried out against PayPay, and to conduct predictive analysis and prepare countermeasures. The Red Team Unit will actively utilize such information to optimize the work of breaking PayPay’s apps and systems. You may now ask, why break the system? One crucial activity in cybersecurity is to detect and fix problems ahead of attackers. The Red Team finds out how to break PayPay’s systems, businesses, and the company itself so that they can find and fix any issues before the attackers do. And these tests are repeated daily using diverse methods. Because the internet is a world where anyone can invade at any time, PayPay has a fighting unit, which helps the company build a solid defense by making the first move and staying ahead of the curve.
Things that were made possible thanks to PayPay’s environment
Business moves really fast at PayPay. The administrative departments like us have to keep up with the pace. For example, we obtained the ISMS and PCI DSS certifications in three months. Getting these certifications involves extensive internal checks, including cross-departmental coordination and surveys, so it was quite a challenge to complete all the reviews in three months. We also often coordinate with outside parties, such as the regulatory authorities, to expedite our work. I see our speed increase every day, driven in part by the Japanese government’s promotion of cashless transactions.
Many projects require approval from the CISO Office, even if they are internal requirements, so it is imperative to make decisions quickly to maintain the company’s business speed. We are also conscious of following up as the second line (administrative teams like us) on points that the speed-oriented first line (development and other hands-on teams) misses.

Maintaining a Secure Information System
Excellent engineers from all over the world
It’s certainly a pleasure to work with the current team members, as they can develop highly sophisticated countermeasures. I’d like to comment on their competence in terms of compliance and governance (information security), as well as cybersecurity.
First, working with information security requires expertise with ISO/IEC, NIST, and security frameworks specialized for the public sector and global finance. The ability to conduct assessments, maturity and supply chain analyses, and familiarity with relevant domestic and international regulations and privacy standards, such as GDPR and CBPR, are a must.
Additionally, cybersecurity requires knowledge of a fairly broad range of disciplines in order to correctly analyze, assess, and counter risks and cyberattacks. A deep understanding of various operating systems, programming languages, mobile and cloud technologies, networks and databases, libraries and frameworks, cryptography and statistics, and log analysis infrastructure (SIEM, SOAR, and UEBA) is required to be able to provide expert and appropriate advice when asked. Plus, familiarity with cyberattack techniques, artifact analysis techniques, and forensic techniques related to all of the above is also important.
Because our members possess these qualifications, we can steadily meet our steep goals every year. Ultimately, the fact that we can deliver safety and security “as usual” to our users makes the team’s work worthwhile.
In addition, cybersecurity often has new information in foreign literature in English, Chinese, Korean, and so forth, so it is an advantage to have colleagues who can speak various languages. We can gather information from diverse sources, which adds depth to our knowledge. Also, team members come up with new ideas, so communication is now a lot of fun. Information from overseas is valuable, as there are large markets outside Japan. So we assign people who can read and understand such sources of information (including their cultural backgrounds). We are proceeding with country risk management regarding information security, hoping to make prudent and flexible decisions by working together with our international teammates.

The future as a leading cashless payment company
The U.S., with its strict regulations, leads the world in security standards for financial institutions. We aim to adopt, conform to, and mature them as quickly as possible. We have positioned the various difficult-to-comply, high-level guidelines as the starting point for our sophistication, and our goal for this year is to comply with global standards at a high level of maturity. To that end, we are first promoting financial institutions to reach the level required from a worldwide perspective. We will also continue to boost our maturity level by considering whether innovative ideas can be attempted in this field. At the same time, we want to make our platform more convenient and secure than cash by keeping up with and responding to constantly evolving attacks.
We are also constantly aware of the balance between a swiftly evolving business and security and the balance between the business and development environments and security. At the same time, we emphasize both security and flexibility. We believe this will help us protect our clients’ assets from various risks and create and maintain a platform that can be used with peace of mind.

For People Who Want to Join
What I value most is the breadth of vision. This work cannot be done without a wide array of knowledge related to information security and cybersecurity, so it is necessary to have a broad perspective and the ability to think flexibly about things from multiple angles. I myself came to PayPay with the motivation to make things safe with my own hands, so the work environment is geared toward those who want to make a difference, are committed to making them happen, and have a strong desire to address various concerns.
If you are not passive and are ready to take action, you will enjoy working at PayPay. This is an excellent place for those who can propel a project forward and those skilled at breaking things, like white hat hackers. So, if you have experience with a broad range and a strong passion, you’re invited to take the plunge and aim high with us!
[Editor’s note]
Before the interview, I had the impression that Nakazawa-san was a very knowledgeable person who could see things from so many vantage points. His diligence and seriousness about security came through in his calm tone while he talked about security during our in-person interview. Nakazawa-san sometimes smiled as he spoke of his team members. I now understand why other members call him an “absolute pro.” I was relieved by PayPay’s extraordinary security measures and really hope that more people will use PayPay.
Current job openings
*The recruitment status is current at the time of the interview.
Special Thanks: Nobuaki Nakazawa / Author & Editor: Danata (PayPay Inside-Out Editorial Team)
*Employees’ affiliations and other information are those at the time of the interview.



